This tutorial is about configuring and using a trojan. There are many
trojans available on internet for free. Some popular ones are Beast, Pro
Rat, Netbus , Back Orifice, Girlfriend, Sub 7. I will be using Pro Rat
in this tutorial.
If you don't know what is trojan. Then Click here for basic understanding of Trojan.
Requirements
-----------------
1. Prorat - Click here to download Trojan Prorat.
2. Hostname -
Your IP address would probably be dynamic that it keeps changing
everytime you disconnect and reconnect. You need a host name which
always
automatically keep pointing to your changing IP.
automatically keep pointing to your changing IP.
Follow these
steps -:
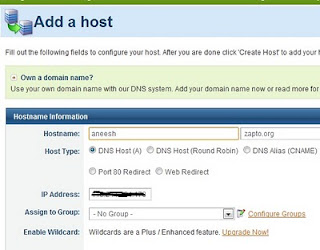
1. Log On to www.no-ip.com and register for an account.
1. Log On to www.no-ip.com and register for an account.
2. Go to Hosts/Redirects; Add Host and choose any free available
hostname.
Do not change any other option and simply click on Create
Host.
3. Downloading and install their DNS update client available here http://www.no-ip.com/downloads.php Run it and enter your credentials. Update your host name and save it.
4. Lets check whether your IP has been associate with chosen host name
or not. Go to command prompt and type 'ping yourhostname' (without
quotes) , hopefully it should reply with your IP address.
Tutorial for configuring Trojan.
1. Open prorat.exe that you have downloaded.
1. Open prorat.exe that you have downloaded.
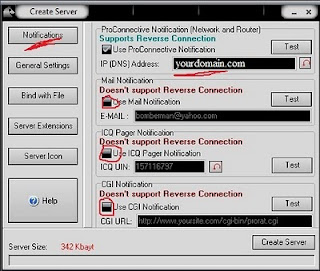
2. Click on Create and then Create ProRat Server
3. Enter your host name in the ProRat Notification field as shown. Uncheck all other options.
4. Click on general settings Tab and have a look at server
port,password, victim name. Remember these things.Check out and
configure other options as per your need. You can bind server.exe with
any genuine file, change its icon etc.
5. Finally click on create server and now its ready to be sent
to victim. Once victim installs it, it would automatically disable
antivirus / firewall.
Modes of sending:
You must be thinking of sending this server.exe to victim through an
email as an attachment but unfortunately you cant do so. The good option
is to upload it on any uploading site like mediafire.com and
give downloading link to victim.
What after victim has run the server part ?
1. Click on Pro-connective Tab and start listening to connections. Allow firewall if it asks
you to open a port.
2. You will start listening to connections, I mean you will get a notification as shown when
victim would be online.
Note: If you know victim is online and still its not listening to
any connections. Trace victim's IP, enter in IP field and hit connect.
But its gonna work only if he is not behind any network and directly
connected to internet. If you don't know how to trace IP, mention in
comments.
What after successful connection ?
After you have managed to connect to
victim's machine. There are numberless interesting things to do.
How to make it undetectable from antivirus ?
Though there isn't any hard and fast way to make it fully undetectable
from all anti-viruses. The real way to do it is modify the source code of
open source Trojans available. Its very challenging job. There are many
crypters which claim to make it undetectable but unfortunately hardly
one out every hundred works. I would try to write next article on the
same.
Countermeasure against Trojans:
The obvious countermeasure against Trojans is that do not accept downloading links blindly. Keep your antivirus up to date.
Detecting and removing Trojan:
Though Trojan once installed is very hard to remove . It would hide itself from the Task Manager.
Install Process Explorer
and it would hopefully show you all process running including Trojan.
Kill the process and remove it. One good thing is to carefully check the
open ports and services running through 'netstat' command.
Anyways ,
the best option is to re-install the windows.
Content From: LH








0 comments:
Post a Comment